This is part 2 of building your own email server from scratch on CentOS/RHEL tutorial series. In part 1, we showed you how to set up a basic Postfix SMTP server. In this tutorial, we are going to configure our email server so that we can receive and send emails using a desktop email client like Mozilla Thunderbird or Microsoft Outlook.
To be able to send emails using a desktop email client, we need to enable the submission service in Postfix. To receive emails using a desktop email client, we can install an open-source IMAP server named Dovecot on CentOS/RHEL server. And to encrypt our communications, we need a TLS certificate.
Open Ports in Firewall
Run the following commands to open email related ports in firewall.
sudo firewall-cmd --zone=public --permanent --add-service={http,https,smtp-submission,smtps,imap,imaps}
sudo systemctl reload firewalld
Securing Email Server Traffic with TLS Certificate
When we configure a desktop email client, enabling encryption is always a good idea. We can easily obtain a free TLS certificate from Let’s Encrypt.
Download Let’s Encrypt client certbot-auto from EFF website.
sudo dnf install wget wget https://dl.eff.org/certbot-auto
Give execute permission.
chmod a x certbot-auto
Move it to user’s PATH, like /usr/local/bin/ and rename it to certbot.
sudo mv certbot-auto /usr/local/bin/certbot
Set root as the owner and change the permission to 0755.
sudo chown root /usr/local/bin/certbot sudo chmod 0755 /usr/local/bin/certbot
If you don’t have a web server running yet, I recommend you install one (Apache or Nginx), because it’s easier to obtain and install TLS certificate with a web server than using other methods. And in a later tutorial, I will show you how to set up webmail, which requires running a web server.
If you prefer Apache, run the following command to install it.
sudo dnf install httpd
Start Apache and enable auto-start at boot time.
sudo systemctl start httpd sudo systemctl enable httpd
If you prefer Nginx, run the following command to install it.
sudo dnf install nginx
Start Nginx and enable auto-start at boot time.
sudo systemctl start nginx sudo systemctl enable nginx
Obtaining TLS Certificate with Apache Web Server
You need to have an Apache virtual host for mail.your-domain.com before obtaining Let’s Encrypt TLS certificate. Create the virtual host file:
sudo nano /etc/httpd/conf.d/mail.your-domain.com.conf
Then paste the following text into the file.
ServerName mail.your-domain.com
DocumentRoot /var/www/html/
Save and close the file. Reload Apache for the changes to take effect.
sudo systemctl reload httpd
Once virtual host is created and enabled, run the following command to obtain and install Let’s Encrypt TLS certificate.
sudo /usr/local/bin/certbot --apache --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d mail.your-domain.com
Substitute the red text with your actual data. If this is a first run on your CentOS/RHEL server, you may be asked to install some dependency packages. Press y to continue.
After a while, you should see the following lines which means the certificate is successfully obtained. You can also see the directory under which your cert is stored.
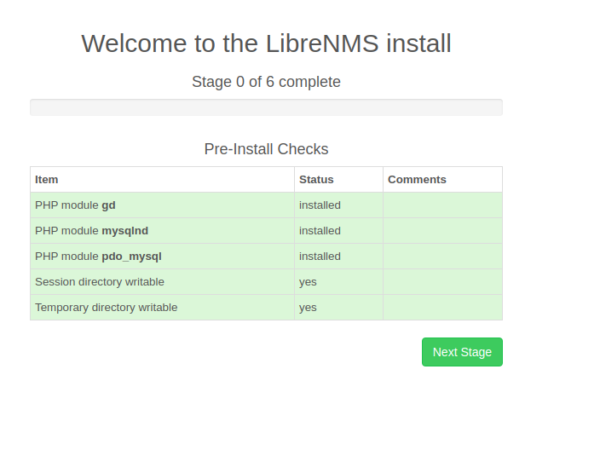
Obtaining TLS Certificate with Nginx Web Server
You need to have an Nginx virtual host for mail.your-domain.com before obtaining Let’s Encrypt TLS certificate. Create the virtual host file:
sudo nano /etc/nginx/conf.d/mail.your-domain.com.conf
Next, paste the following text into the file.
server {
listen 80;
server_name mail.your-domain.com;
root /usr/share/nginx/html/;
location ~ /.well-known/acme-challenge {
allow all;
}
}
Save and close the file. Reload Nginx for the changes to take effect.
sudo systemctl reload nginx
Once virtual host is created and enabled, run the following command to obtain and install Let’s Encrypt certificate with Nginx plugin.
sudo /usr/local/bin/certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d mail.your-domain.com
If this is a first run on your CentOS/RHEL server, you may be asked to install some dependency packages. Press y to continue.
After a while, you should see the following which means the certificate is successfully obtained. You can also see the directory under which your cert is stored.
Configuring Postfix
To send emails from a desktop email client, we need to enable the submission service of Postfix so that the email client can submit emails to Postfix SMTP server. Edit the master.cf file.
sudo nano /etc/postfix/master.cf
In submission section, uncomment or add the following lines. Please allow at least one whitespace (tab or spacebar) before each -o. In postfix configurations, a preceding whitespace character means that this line is continuation of the previous line. (By default the submission section is commented out. You can copy the following lines and paste them into the file, so you don’t have to manually uncomment or add new text.)
submission inet n - y - - smtpd -o syslog_name=postfix/submission -o smtpd_tls_security_level=encrypt -o smtpd_tls_wrappermode=no -o smtpd_sasl_auth_enable=yes -o smtpd_relay_restrictions=permit_sasl_authenticated,reject -o smtpd_recipient_restrictions=permit_mynetworks,permit_sasl_authenticated,reject -o smtpd_sasl_type=dovecot -o smtpd_sasl_path=private/auth
The above configuration enables the submission daemon of Postfix and requires TLS encryption. So later on our desktop email client can connect to the submission daemon in TLS encryption. The submission daemon listens on TCP port 587. STARTTLS is used to encrypt communications between email client and the submission daemon.
Microsoft outlook only supports submission over port 465. If you are going to use Microsoft outlook mail client, then you also need to enable submission service on port 465 by adding the following lines in the file.
smtps inet n - y - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes -o smtpd_sasl_auth_enable=yes -o smtpd_recipient_restrictions=permit_mynetworks,permit_sasl_authenticated,reject -o smtpd_sasl_type=dovecot -o smtpd_sasl_path=private/auth
Save and close the file.
Hint: The SMTP protocol is used when an email client submits emails to an SMTP server.
Next, we need to run the following two commands to specify the location of TLS certificate and private key in Postfix configuration file. Your Let’s Encrypt certificate and private key are stored under /etc/letsencrypt/live/mail.your-domain.com/ directory.
sudo postconf "smtpd_tls_cert_file = /etc/letsencrypt/live/mail.your-domain.com/fullchain.pem" sudo postconf "smtpd_tls_key_file = /etc/letsencrypt/live/mail.your-domain.com/privkey.pem"
If you want to log TLS connections in the mail log (/var/log/maillog), then run the following two commands to enable logging for Postfix.
sudo postconf "smtpd_tls_loglevel = 1" sudo postconf "smtp_tls_loglevel = 1"
Reload Postfix for the changes to take effect.
sudo systemctl reload postfix
If you run the following command, you will see Postfix is now listening on port 587 and 465.
sudo netstat -lnpt | grep master
Installing Dovecot IMAP Server
Enter the following command to install Dovecot on CentOS/RHEL server.
sudo dnf install dovecot
Check Dovecot version:
dovecot --version
Sample output:
2.2.36 (1f10bfa63)
Start Dovecot and enable auto-start at boot time.
sudo systemctl start dovecot sudo systemctl enable dovecot
Configuring Dovecot
First, edit main config file.
sudo nano /etc/dovecot/dovecot.conf
Add the following line to enable IMAP protocol.
protocols = imap
Save and close the file.
Configuring Mailbox Location
mbox is the traditional format for storing emails. Each user’s emails is stored in a single file /var/mail/username. You can run the following command to find the mail spool directory.
postconf mail_spool_directory
Sample output:
mail_spool_directory = /var/mail
The config file for mailbox location is /etc/dovecot/conf.d/10-mail.conf.
sudo nano /etc/dovecot/conf.d/10-mail.conf
Add the following line to use the mbox fomat. (In part 3 of this tutorial series, I will show you how to use the Maildir format with virtual mailbox domains.)
mail_location = mbox:~/mail:INBOX=/var/mail/%u
We also need to add the following line in the file.
mail_privileged_group = mail
Save and close the file. Then add dovecot to the mail group so that Dovecot can read the INBOX.
sudo gpasswd -a dovecot mail
Configuring Authentication Mechanism
Edit the authentication config file.
sudo nano /etc/dovecot/conf.d/10-auth.conf
Uncomment the following line.
disable_plaintext_auth = yes
It will disable plaintext authentication when there’s no SSL/TLS encryption. And if you want to use full email address ([email protected]) to login, add the following line in the file.
auth_username_format = %n
Otherwise, you are able to login with username only (without @your-domain.com). Next, find the following line.
auth_mechanisms = plain
This line only enables the PLAIN authentication mechanism. LOGIN is another authentication mechanism you probably want to add to support older email clients.
auth_mechanisms = plain login
Configuring SSL/TLS Encryption
Next, edit SSL/TLS config file.
sudo nano /etc/dovecot/conf.d/10-ssl.conf
You can find the following line, which requires email clients to communicate with Dovecot with TLS encryption.
ssl = required
Then find the following two lines.
ssl_cert = </etc/pki/dovecot/certs/dovecot.pem ssl_key = </etc/pki/dovecot/private/dovecot.pem
We need to replace values with the location of your SSL/TLS cert and private key. Don’t leave out the < character. It’s necessary.
ssl_cert = </etc/letsencrypt/live/mail.your-domain.com/fullchain.pem ssl_key = </etc/letsencrypt/live/mail.your-domain.com/privkey.pem
Save and close the file.
SASL Authentication Between Postfix and Dovecot
Edit the following file.
sudo nano /etc/dovecot/conf.d/10-master.conf
Change service auth section to the following so that Postfix can find the Dovecot authentication server.
service auth {
unix_listener /var/spool/postfix/private/auth {
mode = 0660
user = postfix
group = postfix
}
}
Auto-create Sent and Trash Folder
Edit the below config file.
sudo nano /etc/dovecot/conf.d/15-mailboxes.conf
To auto-create a folder, simply add the following line in the mailbox section.
auto = create
Example:
mailbox Trash {
auto = create
special_use = Trash
}
Some common folders you will want to create includes: Drafts, Junk, Trash and Sent. These folders will be created at the user’s home directory. After you save and close all above config files, restart Dovecot.
sudo systemctl restart dovecot
Dovecot will be listening on port 143 (IMAP) and 993 (IMAPS), as can be seen with:
sudo netstat -lnpt | grep dovecot
If there’s a configuration error, dovecot will fail to restart, so it’s a good idea to check the status of Dovecot.
systemctl status dovecot
We also need to restart Postfix to allow the LOGIN authentication mechanism.
sudo systemctl restart postfix
Configure Desktop Email Client
Now open up your desktop email client such as Mozilla Thunderbird and add a mail account.
- In the incoming server section, select IMAP protocol, enter
mail.your-domain.comas the server name, choose port 143 and STARTTLS. Choosenormal passwordas the authentication method. - In the outgoing section, select SMTP protocol, enter
mail.your-domain.comas the server name, choose port 587 and STARTTLS. Choosenormal passwordas the authentication method.
Hint: You can also use port 993 with SSL/TLS encryption for IMAP, and use port 465 with SSL/TLS encryption for SMTP
You should now be able to connect to your own email server and also send and receive emails with your desktop email client!
Using Dovecot to Deliver Email to Message Store
By default, Postfix uses its builtin local delivery agent (LDA) to move inbound emails to the message store (inbox, sent, trash, Junk, etc). We can configure it to use Dovecot to deliver emails, via the LMTP protocol, which is a simplified version of SMTP. LMTP allows for a highly scalable and reliable mail system. This step is required if you want to use the sieve plugin to filter inbound messages to different folders.
Edit the Dovecot main configuration file.
sudo nano /etc/dovecot/dovecot.conf
Add lmtp to the supported protocols.
protocols = imap lmtp
Save and close the file. Then edit the Dovecot 10-master.conf file.
sudo nano /etc/dovecot/conf.d/10-master.conf
Change the lmtp service definition to the following.
service lmtp {
unix_listener /var/spool/postfix/private/dovecot-lmtp {
group = postfix
mode = 0600
user = postfix
}
}
Next, edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following lines at the end of the file. The first line tells Postfix to deliver emails to local message store via the dovecot LMTP server. The second line disables SMTPUTF8 in Postfix, because Dovecot-LMTP doesn’t support this email extension.
mailbox_transport = lmtp:unix:private/dovecot-lmtp smtputf8_enable = no
Save and close the file. Finally, restart Postfix and Dovecot.
sudo systemctl restart postfix dovecot
Wrapping Up
I hope this article helped you set up Postfix and Dovecot on CentOS/RHEL server. In part 3, I will show you how to create virtual mailboxes on CentOS/RHEL with PostfixAdmin. If you want to access emails via Webmail, then I recommend RainLoop Webmail, which is lightweight, fast and has a modern interface. Roundcube is also a popular open source webmail client.
Rate this tutorial
[Total: 0 Average: 0]