Suricata is a free and open-source network analysis and threat detection software developed by OSIF. It can be used as an intrusion detection system (IDS) and an intrusion prevention system (IPS). It uses a rule set and signature language to detect and prevent threats. It is an alternative to Snort and can provide great insight into what is occurring on your network from a security perspective.
In this tutorial, I will show you how to install Suricata on Ubuntu 22.04 server.
Requirements
- A server running Ubuntu 22.04.
- A root password is configured on your server.
Getting Started
Before starting, it is a good idea to update your system packages to the latest version. You can update all of them by running the following command:
apt update -y
apt upgrade -y
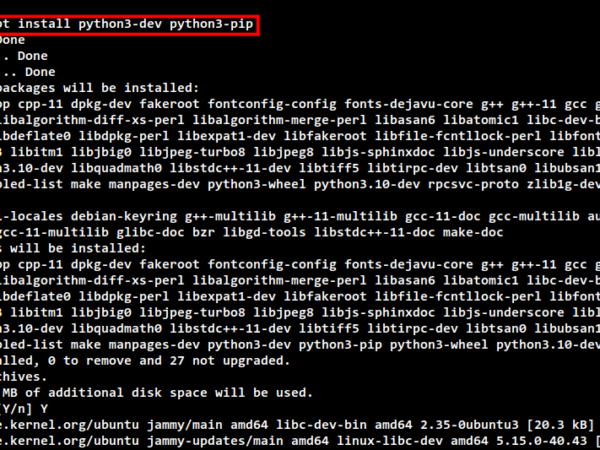
Once all the packages are updated, run the following command to install all the required dependencies:
apt install libpcre3 libpcre3-dbg libpcre3-dev build-essential autoconf automake libtool libpcap-dev libnet1-dev libyaml-0-2 libyaml-dev zlib1g zlib1g-dev libcap-ng-dev libcap-ng0 make libmagic-dev libjansson-dev libjansson4 pkg-config libnspr4-dev libnss3-dev liblz4-dev rustc cargo python3-pip python3-distutils
apt install libnetfilter-queue-dev libnetfilter-queue1 libnfnetlink-dev libnfnetlink0
Once you are finished, you can proceed to the next step.
Install Suricata from Source
First, download the latest version of Suricata with the following command:
wget https://www.openinfosecfoundation.org/download/suricata-6.0.8.tar.gz
Once the download is completed, extract the downloaded file with the following command:
tar xzf suricata-6.0.8.tar.gz
Next, navigate to the extracted directory and configure it with the following command:
cd suricata-6.0.8
./configure --enable-nfqueue --prefix=/usr --sysconfdir=/etc --localstatedir=/var
You will get the following output:
Host: x86_64-pc-linux-gnu
Compiler: gcc (exec name) / g (real)
GCC Protect enabled: no
GCC march native enabled: yes
GCC Profile enabled: no
Position Independent Executable enabled: no
CFLAGS -g -O2 -std=c11 -march=native -I${srcdir}/../rust/gen -I${srcdir}/../rust/dist
PCAP_CFLAGS -I/usr/include
SECCFLAGS
To build and install run 'make' and 'make install'.
You can run 'make install-conf' if you want to install initial configuration
files to /etc/suricata/. Running 'make install-full' will install configuration
and rules and provide you a ready-to-run suricata.
To install Suricata into /usr/bin/suricata, have the config in
/etc/suricata and use /var/log/suricata as log dir, use:
./configure --prefix=/usr/ --sysconfdir=/etc/ --localstatedir=/var/
Next, install the Suricata with the following command:
make
make install-full
You will get the following output:
You can now start suricata by running as root something like: /usr/bin/suricata -c /etc/suricata/suricata.yaml -i eth0 If a library like libhtp.so is not found, you can run suricata with: LD_LIBRARY_PATH=/usr/lib /usr/bin/suricata -c /etc/suricata/suricata.yaml -i eth0 The Emerging Threats Open rules are now installed. Rules can be updated and managed with the suricata-update tool. For more information please see: https://suricata.readthedocs.io/en/latest/rule-management/index.html make[1]: Leaving directory '/root/suricata-6.0.8'
Install Suricata from Ubuntu Repository
You can also install the Suricata from the Ubuntu repository. First, install all the dependencies using the following command:
apt install gnupg2 software-properties-common curl wget git unzip -y
Next, add the Suricata repository with the following command:
add-apt-repository ppa:oisf/suricata-stable --yes
Next, update the repository cache with the following command:
apt update
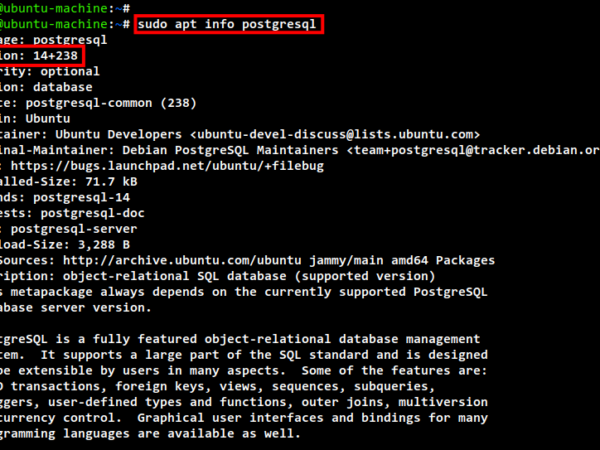
Next, verify the Suricata package with the following command:
apt-cache policy suricata
You will get the following output:
suricata:
Installed: (none)
Candidate: 1:6.0.4-3
Version table:
1:6.0.4-3 500
500 http://us.archive.ubuntu.com/ubuntu jammy/universe amd64 Packages
Finally, install the Suricata with the following command:
apt install suricata jq
You can now verify the Suricata package information using the following command:
suricata --build-info
You should get the following output:
This is Suricata version 6.0.8 RELEASE Features: NFQ PCAP_SET_BUFF AF_PACKET HAVE_PACKET_FANOUT LIBCAP_NG LIBNET1.1 HAVE_HTP_URI_NORMALIZE_HOOK PCRE_JIT HAVE_NSS HAVE_LIBJANSSON TLS TLS_C11 MAGIC RUST SIMD support: SSE_3 Atomic intrinsics: 1 2 4 8 16 byte(s) 64-bits, Little-endian architecture GCC version 11.2.0, C version 201112 compiled with _FORTIFY_SOURCE=2 L1 cache line size (CLS)=64 thread local storage method: _Thread_local compiled with LibHTP v0.5.41, linked against LibHTP v0.5.41 Suricata Configuration: AF_PACKET support: yes eBPF support: no XDP support: no PF_RING support: no NFQueue support: yes NFLOG support: no IPFW support: no Netmap support: no DAG enabled: no Napatech enabled: no WinDivert enabled: no Unix socket enabled: yes Detection enabled: yes
Configure Suricata
Next, edit the Suricata configuration file and define your network interface and network:
nano /etc/suricata/suricata.yaml
Change the following lines:
HOME_NET: "[10.0.2.0/24]"
EXTERNAL_NET: "!$HOME_NET"
af-packet:
- interface: eth0
# - sip
sip:
enabled: no
Save and close the file then update the Suricata configuration with the following command:
suricata-update
Next, verify the Suricata configuration file with the following command:
suricata -T -c /etc/suricata/suricata.yaml -v
You will get the following output:
18/10/2022 -- 13:45:14 - - fast output device (regular) initialized: fast.log 18/10/2022 -- 13:45:14 - - eve-log output device (regular) initialized: eve.json 18/10/2022 -- 13:45:14 - - stats output device (regular) initialized: stats.log 18/10/2022 -- 13:45:14 - - SSSE3 support not detected, disabling Hyperscan for SPM 18/10/2022 -- 13:45:16 - - 1 rule files processed. 28624 rules successfully loaded, 0 rules failed 18/10/2022 -- 13:45:16 - - Threshold config parsed: 0 rule(s) found 18/10/2022 -- 13:45:16 - - 28627 signatures processed. 1219 are IP-only rules, 5166 are inspecting packet payload, 22038 inspect application layer, 108 are decoder event only 18/10/2022 -- 13:45:19 - - Configuration provided was successfully loaded. Exiting. 18/10/2022 -- 13:45:19 - - cleaning up signature grouping structure... complete
Next, start and enable the Suricata service with the following command:
systemctl enable --now suricata
You can also check the Suricata service with the following command:
systemctl status suricata
You should see the following output:
? suricata.service - LSB: Next Generation IDS/IPS
Loaded: loaded (/etc/init.d/suricata; generated)
Active: active (running) since Tue 2022-10-18 13:38:52 UTC; 6min ago
Docs: man:systemd-sysv-generator(8)
Process: 16504 ExecStart=/etc/init.d/suricata start (code=exited, status=0/SUCCESS)
Tasks: 7 (limit: 2242)
Memory: 40.0M
CPU: 4.073s
CGroup: /system.slice/suricata.service
??16514 /usr/bin/suricata -c /etc/suricata/suricata.yaml --pidfile /var/run/suricata.pid --af-packet -D -vvv
Oct 18 13:38:52 ubuntu2204 systemd[1]: Starting LSB: Next Generation IDS/IPS...
Oct 18 13:38:52 ubuntu2204 suricata[16504]: Starting suricata in IDS (af-packet) mode... done.
Oct 18 13:38:52 ubuntu2204 systemd[1]: Started LSB: Next Generation IDS/IPS.
You can also see various run modes using the following command:
suricata --list-runmodes
You will get the following output:
------------------------------------- Runmodes ------------------------------------------ | RunMode Type | Custom Mode | Description |---------------------------------------------------------------------------------------- | PCAP_DEV | single | Single threaded pcap live mode | --------------------------------------------------------------------- | | autofp | Multi threaded pcap live mode. Packets from each flow are assigned to a single detect thread, unlike "pcap_live_auto" where packets from the same flow can be processed by any detect thread | --------------------------------------------------------------------- | | workers | Workers pcap live mode, each thread does all tasks from acquisition to logging |---------------------------------------------------------------------------------------- | PCAP_FILE | single | Single threaded pcap file mode | --------------------------------------------------------------------- | | autofp | Multi threaded pcap file mode. Packets from each flow are assigned to a single detect thread, unlike "pcap-file-auto" where packets from the same flow can be processed by any detect thread |---------------------------------------------------------------------------------------- | PFRING(DISABLED) | autofp | Multi threaded pfring mode. Packets from each flow are assigned to a single detect thread, unlike "pfring_auto" where packets from the same flow can be processed by any detect thread | --------------------------------------------------------------------- | | single | Single threaded pfring mode | --------------------------------------------------------------------- | | workers | Workers pfring mode, each thread does all tasks from acquisition to logging |----------------------------------------------------------------------------------------
Verify Suricata
Before verifying Suricata, you will need to disable the packet offload features on the network interface.
You can disable it with the following command:
ethtool -K eth0 gro off lro off
Next, stop the Suricata with the following command:
systemctl stop suricata
rm -rf /var/run/suricata.pid
Next, run the Suricata manually using the following command:
suricata -D -c /etc/suricata/suricata.yaml -i eth0
Next, log in to the remote system and run the hping3 command to perform a simple DDoS attack against the Suricata server:
hping3 -S -p 80 --flood --rand-source suricata-ip -I eth0 -c 50
Next, go back to the Suricata server and check the Suricata log file:
tail -f /var/log/suricata/fast.log
You should see the following output:
10/18/2022-14:01:38.569298 [**] [1:2210008:2] SURICATA STREAM 3way handshake SYN resend different seq on SYN recv [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 157.32.37.21:59188 -> 209.23.10.188:80
10/18/2022-14:01:38.569304 [**] [1:2210004:2] SURICATA STREAM 3way handshake SYNACK resend with different ack [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 209.23.10.188:80 -> 157.32.37.21:59188
10/18/2022-14:01:38.569649 [**] [1:2210008:2] SURICATA STREAM 3way handshake SYN resend different seq on SYN recv [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 157.32.37.21:53343 -> 209.23.10.188:80
10/18/2022-14:01:38.569655 [**] [1:2210004:2] SURICATA STREAM 3way handshake SYNACK resend with different ack [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 209.23.10.188:80 -> 157.32.37.21:53343
10/18/2022-14:01:38.570762 [**] [1:2210008:2] SURICATA STREAM 3way handshake SYN resend different seq on SYN recv [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 157.32.37.21:62070 -> 209.23.10.188:80
10/18/2022-14:01:38.570770 [**] [1:2210004:2] SURICATA STREAM 3way handshake SYNACK resend with different ack [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 209.23.10.188:80 -> 157.32.37.21:62070
10/18/2022-14:01:38.571748 [**] [1:2210008:2] SURICATA STREAM 3way handshake SYN resend different seq on SYN recv [**] [Classification: Generic Protocol Command Decode] [Priority: 3] {TCP} 157.32.37.21:5001 -> 209.23.10.188:80
Conclusion
In this post, you learned how to install Suricata on Ubuntu 22.04. You can now implement Suricata in your organization to protect your servers from DDoS attacks. Feel free to ask me if you have any questions.